Edit : have subsequently extended the capsh for additional hardening i.e capsh command now looks like
capsh --drop=cap_chown,cap_sys_admin,cap_sys_chroot,
cap_net_admin,cap_net_bind_service,cap_sys_boot,
cap_sys_module,cap_sys_resource,cap_setpcap,cap_setgid,
cap_setuid,cap_sys_rawio,cap_mknod,cap_net_raw,
cap_audit_control,cap_mac_override,cap_mac_admin,
cap_syslog,cap_audit_read,cap_audit_write,cap_fsetid --keep=1 --user=rover --uid=1003 -- -c /bin/sh --
EasyOS Pyro 0.9
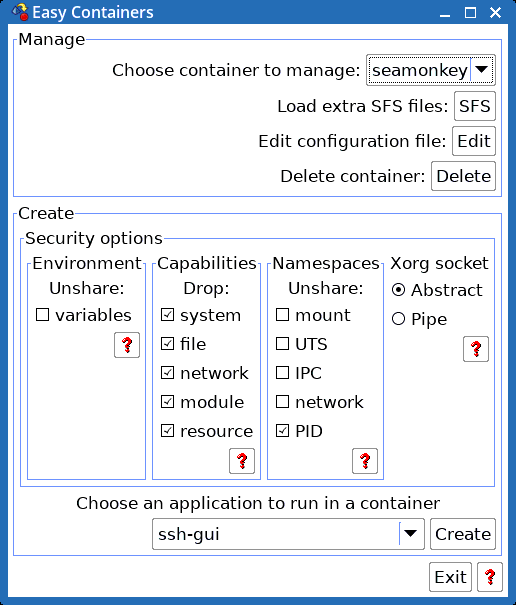
Create a sakura container (see attached images and note in particular you have to untick the USER option when creating the container).
Once created a desktop icon will be shown for that new sakura container, click on that to open it and then cd /root and replace the current .bashrc file content with the following
Code: Select all
###################################################
#
# Rufwoof April 2018
#
# /root/.bashrc file for EasyOS Pyro 0.9 container
# set so that it runs a /bin/sh as restricted userid
# 'rover' under capsh that restricts root from
# from chown sys_admin and chroot i.e. running exit-chroot
# as root just puts you back to the / folder of the container
#
# Goes some way to thwart hacks such as escaping the chroot
# container and/or elevating privileges
#
###################################################
. /etc/profile
#v1.0.5 need to override TERM setting in /etc/profile...
#export TERM=xterm
# ...v2.13 removed.
#export HISTFILESIZE=2000
#export HISTCONTROL=ignoredups
#...v2.13 removed.
#Number SIG Meaning
#0 0 On exit from shell
#1 SIGHUP Clean tidyup
#2 SIGINt Interrupt
#3 SIGQUIT Quit
#6 SIGABRT Abort
#15 SIGTERM Terminate
trap finish 0 1 2 3 6 15
finish()
{
exit
}
chmod 700 /root
chmod 000 /usr/sbin/gparted
chmod 000 /sbin/fdisk
# ... etc for any other individual file/folders you wish to restrict
HOME=/home/rover export HOME
DISPLAY=:0 export DISPLAY
XDG_DATA_HOME=/home/rover/.local/share
GTK2_RC_FILES=/home/rover/.gtkrc-2.0
USER=rover
PATH=/bin:/usr/bin:/sbin:/usr/sbin:/usr/local/bin
XFINANSDIR=/home/rover/.xfinans
XDG_CONFIG_HOME=/home/rover/.config
XDG_CACHE_HOME=/home/rover/.cache
LOGNAME=rover
cd /home/rover
capsh --drop=cap_chown,cap_sys_admin,cap_sys_chroot --user=rover --uid=1003 -- -c /bin/sh --
# For root level (testing) uncomment the following and comment out the above
#capsh --drop=cap_chown,cap_setuid,cap_sys_admin,cap_sys_chroot -- -c /bin/sh --
exit
Add rover to the audio group so that you'll hear sounds when playing videos in your browser
Also navigate to /usr/bin and edit seamonkey to change the code that looks like
Code: Select all
if [ "$NAMEOFUSER" == "spot" ];then
HOMEDIR="/root/spot/.mozilla/seamonkey"
NAMEEXE='seamonkey.bin'
else #called as seamonkey or mozilla...
HOMEDIR="/root/.mozilla/seamonkey"
NAMEEXE='seamonkey'
fi
to look like
Code: Select all
if [ "$NAMEOFUSER" == "spot" ];then
HOMEDIR="/root/spot/.mozilla/seamonkey"
NAMEEXE='seamonkey.bin'
else
if [ "$NAMEOFUSER" == "rover" ];then
HOMEDIR="/home/spot/.mozilla/seamonkey"
NAMEEXE='seamonkey.bin'
else #called as seamonkey or mozilla...
HOMEDIR="/root/.mozilla/seamonkey"
NAMEEXE='seamonkey'
fi
fi
EDIT : THERE IS A ISSUE WITH THE ORANGE SEAMONKEY SPLASH SCREEN SHOWING FOR A LONG TIME ... SEE NEXT POST
Also edit /etc/profile.d/pup_gtk and change the content from
Code: Select all
export GTK2_RC_FILES=/root/.gtkrc-2.0
to
Exit the container ... and then open the container again by clicking the desktop icon. The first time you opened the container you were running as root, as you will be the second/subsequent times, however root .bashrc is now set to throw you into rover, along with having set up restrictions i.e. dropping root out of certain operations and commands etc.
At the command prompt type seamonkey and press enter. Seamonkey will open and you'll be running it inside a container, running as user 'rover' and having capsh and other file/executable permissions that would make it more difficult for hackers to penetrate your system via seamonkey. Note however that if you save/download files etc then they are saved inside the container (as per any other container).
Once initially set up, if you create a snapshot of that sakura container, you can simply roll back to that whenever you want a nice clean container again (see the 'containers' section in Menu, FileSystem, Easy Version Control).
So now you can run a shell prompt session inside a container... and start seamonkey and be running as rover that has limited permissions. If a known vulnerability in your browser is exploited when visiting a dubious web site then they'll drop to the userid that the browser was running under i.e. rover ... which is a restricted user. They might try and elevate their permissions by using weaknesses in the main filesystem ... and if they do find one and gain root access then they're still locked into the container and where root also has restrictions as what it can do - including being blocked from chroot'ing out of the chroot container.